Before you click ‘Apply;’ understanding the job post phishing epidemic

Phishers and scammers never miss a trick. Fraudulent job listings are just the latest scheme in their long list of dastardly doings.
Read More4 Tips for Giving the Gift of Technology This Holiday Season

With the holiday season in full swing, many are scrambling to find last-minute gifts and check off the items already on their list. For many, technology and smart devices are a simple but popular gift for family and friends. However, these devices come with a great deal of responsibility, as well as dangers. Keep reading to learn more about how you can ensure your loved ones are appropriately prepped for that new iPad, Kindle or laptop that’s sitting wrapped under the tree.
Read MoreMoodle Update Brings Helpful New Features

The most recent Moodle update boasts an impressive suite of new features and tools to make teaching easier. From grading to course management, there’s a lot to get excited about.
Read MoreCybersecurity & You: A Conversation with Director Sheehan
If you’ve been following us on social media, you likely already know – October is Cybersecurity Awareness Month. And who better to learn from about the topic than Mr. Phishead himself – Information Security Director Gary Sheehan?
Read MoreElon Nursing Students Help Pioneer E-Connect Apple iPad Initiative
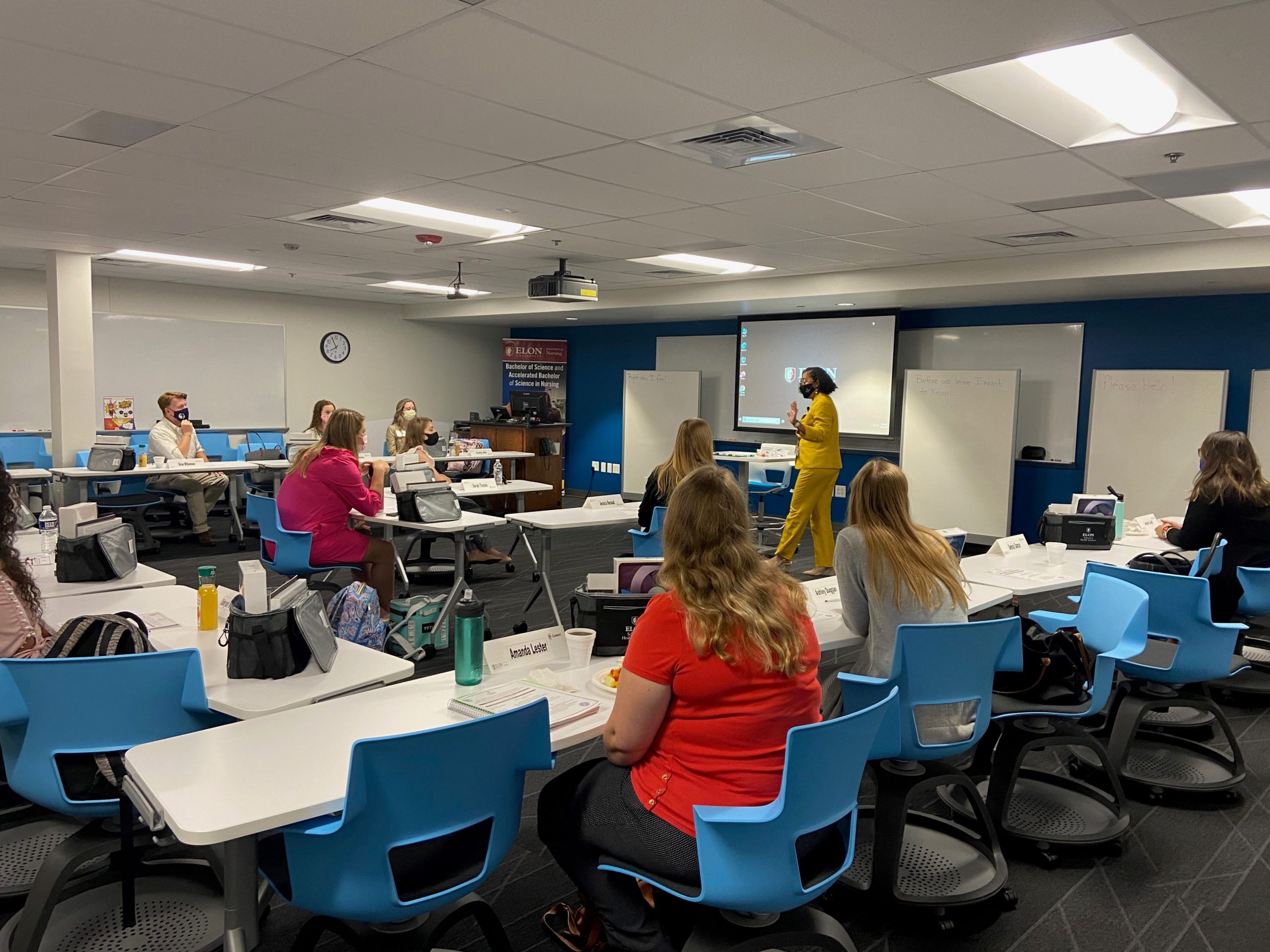
Elon University embraces innovation on all fronts — and the School of Health Sciences is taking things to another level with its brand-new Nursing department.
Read MorePegasus Spyware Illustrates Importance of Updating iOS Devices
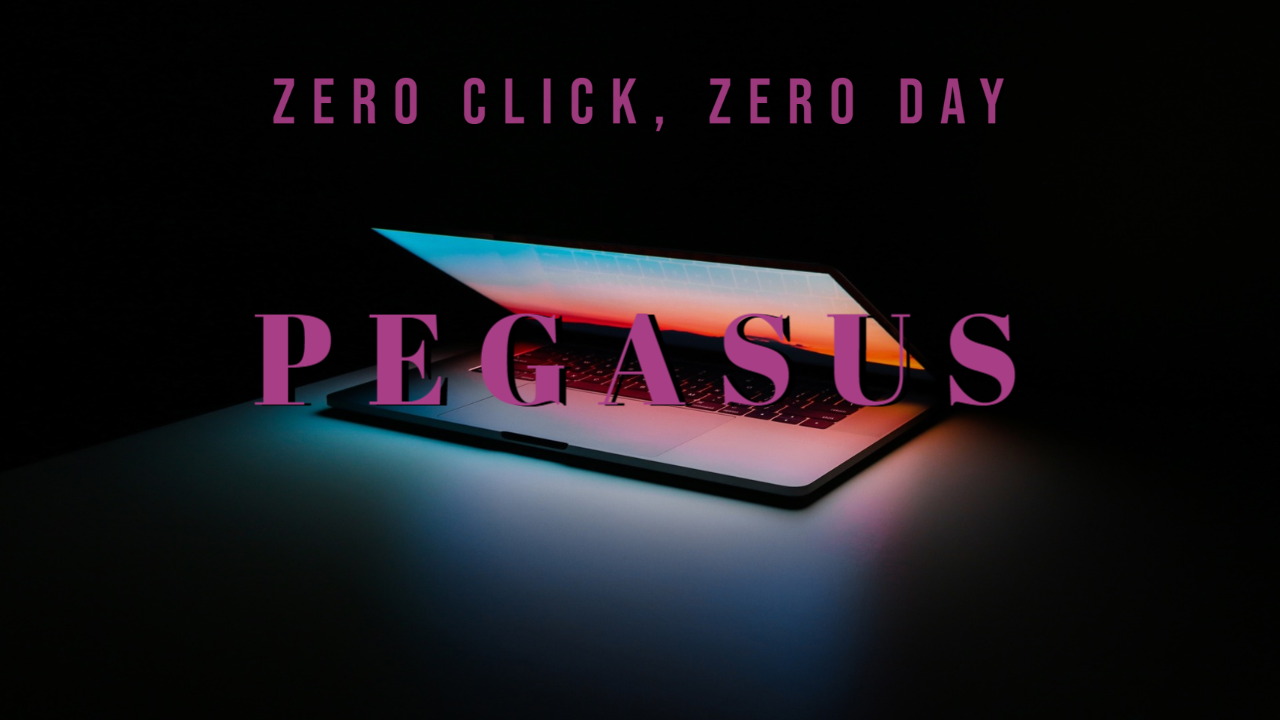
Earlier this week, Apple released iOS 15. The new operating system arrived only a week after the tech giant rolled out iOS 14.8 and other updates for their devices to counter an aggressive new spyware called “Pegasus.”
Read MoreAlert: A Tricky New Phishing Caper
A new pandemic-themed phishing campaign is making the rounds. This particular scam exploits the ongoing uncertainty that many have when it comes to their organization’s COVID-19 policies, according to Roger Kay at INKY. Emails claiming to be from Human Resources (and sent from a compromised email account) are being sent to employees of various organizations telling them that they’re being required to fill out a COVID-19 vaccination status form. This is also known as “Form Phishing.” However, when the user clicks on the link in the email, they’re directed to a fake Microsoft Outlook credential phishing page. This is a tactic known as “brand impersonation,” which uses elements of a well-known brand to make an email look as if it came from that company. In this case, the brand being imitated was Microsoft Outlook. Because these emails come from legitimate but compromised (or “hacked”) accounts, they are able to pass…
Read MoreTechnology Workshops for September 2021
As a part of Elon’s commitment to lifelong learning and supporting faculty and staff development, Information Technology is offering a variety of workshops during the month of September.
Read MoreTechnology at Elon: The Basics
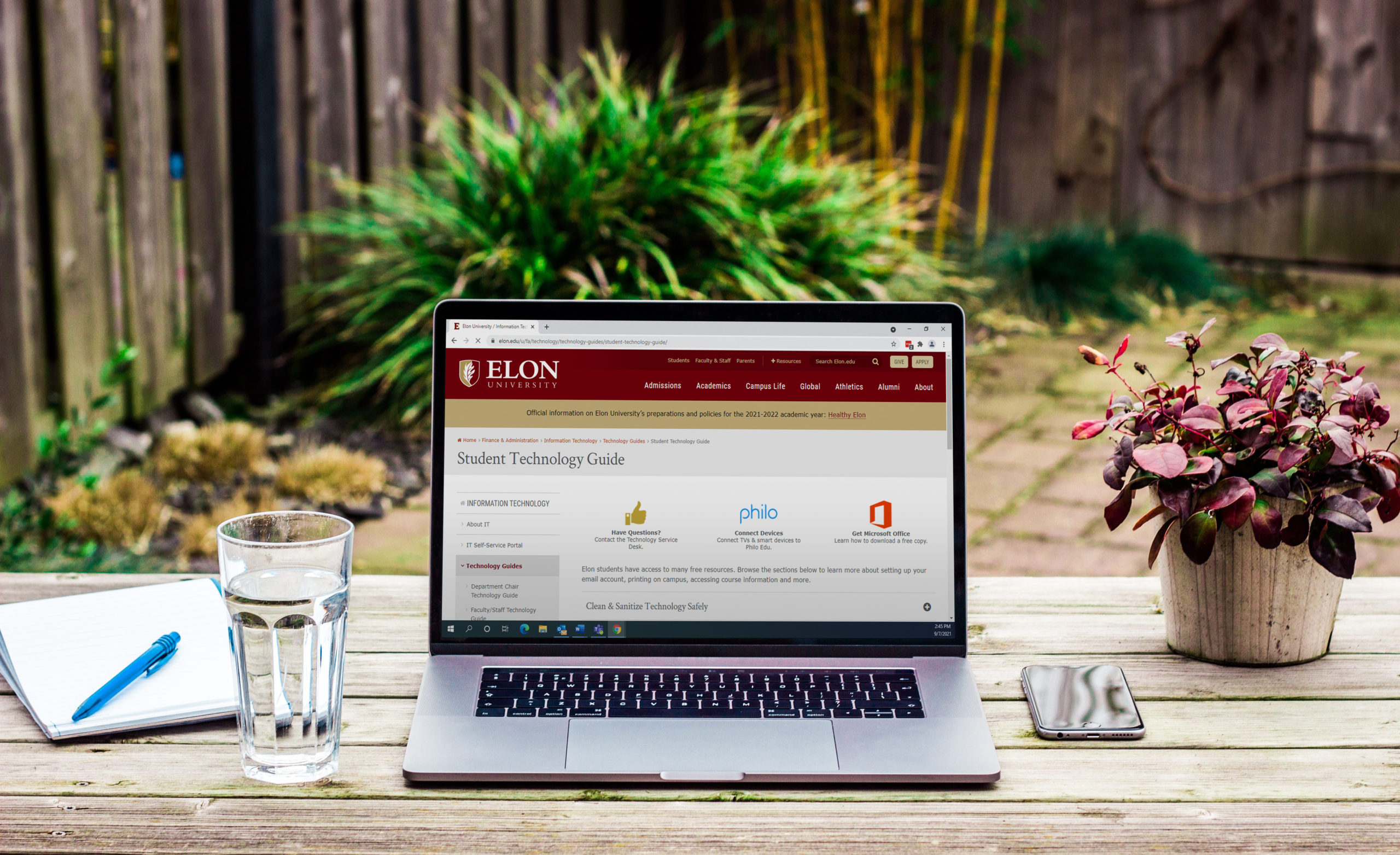
Starting college can be an intimidating prospect, even weeks after your first class. There’s a lot of new information to learn, and that’s not even including the classes! We’ve distilled some of the important information related to technology here at Elon for you in this blog to help you get adjusted to campus life at Elon.
Read More17th Annual Teaching and Learning Conference: Registration Open

Register for this free, virtual conference happening on June 10th.
Read More